Touching base, one month in
Miguel Martinez
Hi!
It’s been a bit over a month since we launched our private beta and today we are happy to announce that Chainloop is now in public beta!
We couldn’t be happier with the feedback we’ve received so far. Granted we’ve not been flooded by its quantity, but the quality of it was outstanding. Thanks to everyone who took the time to share such thoughtful and detailed pieces of feedback, you rock!
Now it’s our turn to give you an update on the product direction based on some of the recurring themes.
I’ve read the docs but I am confused about the tooling and each team ownership
The idea is that SecOps teams have access to a centralized control-plane/single source of truth where they can define workflow contracts, audit attestation/artifacts and so on. Development teams, on the other hand, just need to use the chainloop attestation CLI to integrate their CI/CD pipelines.
We know we can do a better job at communicating, documenting and splitting concerns, that’s why we are working on:
- Role-explicit guides, such as this operator reference.
- Splitting Chainloop’s CLI into an administration CLI for Ops and attestation CLI for devs.
- Building a new Web User Interface for Operators. To simplify workflow onboarding, contract handling and enable observability features.
My attestations and artifacts are being ingested, now what?
By integrating your CI/CD systems with Chainloop you get SLSA provenance level 3 compliant attestation plus intermediate artifacts/materials stored in a standardized central location (your OCI registry). You can then use any OCI-compatible client to handle those artifacts.
But to us, attestation/artifact ingestion is just the beginning, a pre-requisite(that happens to be nice to have for compliance purposes :) for what will be coming next.
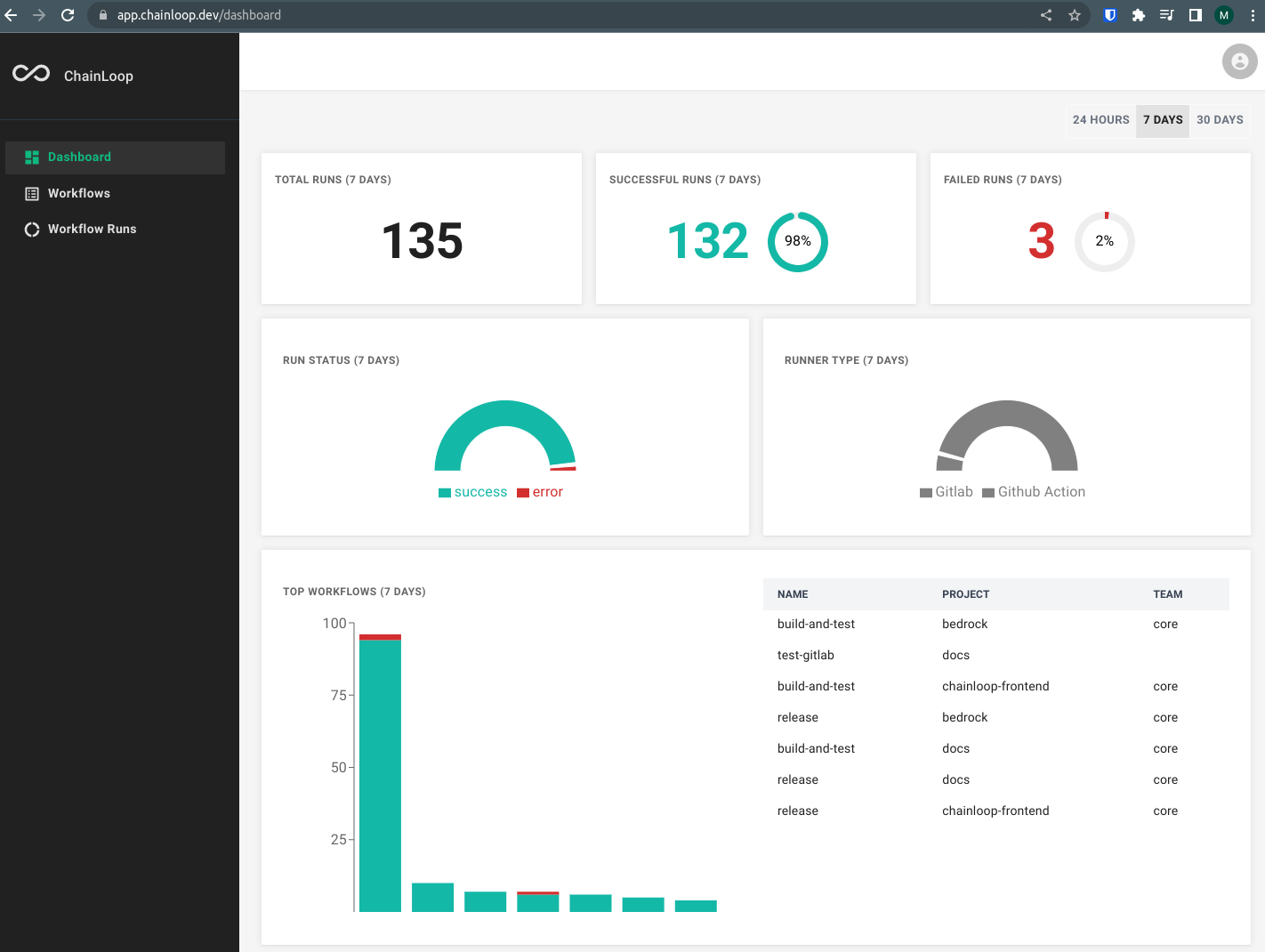
- Workflow-related metrics to detect anomalies and readiness issues in your Software Supply Chain. Some of those metrics can be found already in our Beta web UI.
- We are working on integrating with third parties such as
Dependency Track
. That way, Software Bill of Materials (SBOMs) sent to Chainloop can be forwarded to dep-track for analysis. - We are looking into offering rule and notification mechanisms to define Software Supply Chain Service Level Objectives (SLOs). No more undetected, broken CI Jobs!
Is Chainloop Open Source? I want to run my own instance
UPDATE
Chainloop is now Open Source! 🎉
Read more in our announcement post
We are committed to making Chainloop Open source, we are figuring out the details. Stay tuned!
I am using neither GitHub Actions nor Gitlab, can I still use Chainloop?
Yes, Chainloop is runner agnostic, the Workflow Contract can define the materials, environment variables you want your attestation to have.
That said, Chainloop has an optional feature called Runner Context that automatically will add a set of pre-defined env variables and will enforce the attestation to happen in that environment.
You can still use Chainloop without setting a runner context but we are committed to adding as many CI/CD runners as possible so please Contact us with your preference and we will get back to you.
It’s hard to follow the project’s progress
Until we figure out the Open Source bits, we’ve put in place a Changelog with a high-level summary and the latest user-facing changes.
Closing thoughts
We are very proud of what we’ve accomplished in the last couple of months and can’t wait to see what we can achieve together.
Thanks again and remember, send any thoughts or pieces of feedback our way!
Cheers, Miguel


